Security Systems Planning & Design
Physical Barriers | Electronic Security Systems | Information, Cyber & Cloud Security
Match Equipment & Designs To Needs
Harmonize Designs, Measures & Operations
Estimate Costs & Optimize Your Budget
Avoid Hidden Costs & Technical Surprises
Procure & Deploy To Industry Standards
At Goldmark Security Consulting, we offer a range of security design and professional services spanning multiple domains.
Our multi-faceted approach to security planning and design is intended to help organizations of all sizes overcome the many challenges and complexities involved in the process.
We offer a comprehensive and systematic approach to help organizations address the business and technological interdependencies between the physical, information, and cyber security domains, and in short:
Minimize the likelihood of an undesirable security event
Our goal is to optimize your overall benefit and simplify the many complexities involved in the process. Ultimately our aim is to help you with cost-effective security solutions that align with your organization's risk appetite, goals, and the realities of modern threats.
Tailored Strategy
Security needs are different and vary with industry, regulatory requirements, existing elements and controls, business environments, objectives, specific threats, budget, and risk appetite that dictate unique solutions to your business. We work closely with you, listening to your concerns, and understanding your ultimate business objectives to determine the optimal strategies and solutions that align with your business goals and fit your needs and budget.
Risk-Based Approach
The assessment complexity of the various domains can be a daunting task for any organization. While achieving a 100% secure state is not only costly but also unrealistic, we bring in a practical risk-based approach to assessing your various programs (such as policies, procedures, technologies, integrations, operations, and controls). We help you identify the hidden risks, analyze its impact and provide you with meaningful insights for making informed decisions and managing them effectively.
Whether you have adopted established frameworks, principals and guidelines such as ISO, NIST, COSO, ANSI/ASIS/RIMS, have your own, or looking into adopting industry best practices and guidelines that fit your organizational goals, budget, and objectives; we can help you.
We help you create and capture value through a unified risk assessment approach to managing your information, cyber and physical security risks, analyzing gaps, enabling your compliance requirements, and providing a prioritized risk treatment plan that meets your business objectives.
To Learn More!
ctbybyvbybvyb yvhvyh
The Design & Planning Process
Define Requirements
Whether you have a new, existing, or a retrofit security project, we work with you to capture, review, analyze, evaluate and define the security requirements, business processes and overall needs. From baseline to advanced security requirements, we help you capture the many related elements and essential dependencies to define the scope, optimize your investment, and align your project with your overall business goals.
Design Development (SD, DD)
Maximize your investment and security resources with value-added design services from conception, development, to completion. Benefit from a comprehensive design and due diligence approach that brings together your technology, processes, and management across your physical, IT, Cyber and security management operations. A unified approach tailored to your business strategies, and to closing security gaps between programs, technologies, and processes.
Bid Documentation & Support
Leverage our expertise, and connections with manufacturers, system integrators and industry specialists for all stages of you project contractual and acquisition phases. Whether you are looking for the best procurement approach or looking for professionally-written RFP documentation, we can help you. Get the expert guidance, and robust industry-compliant contractual documentation that protects your investment and helps you compare, negotiate and select contracts fairly and transparently.
Project Management & Support
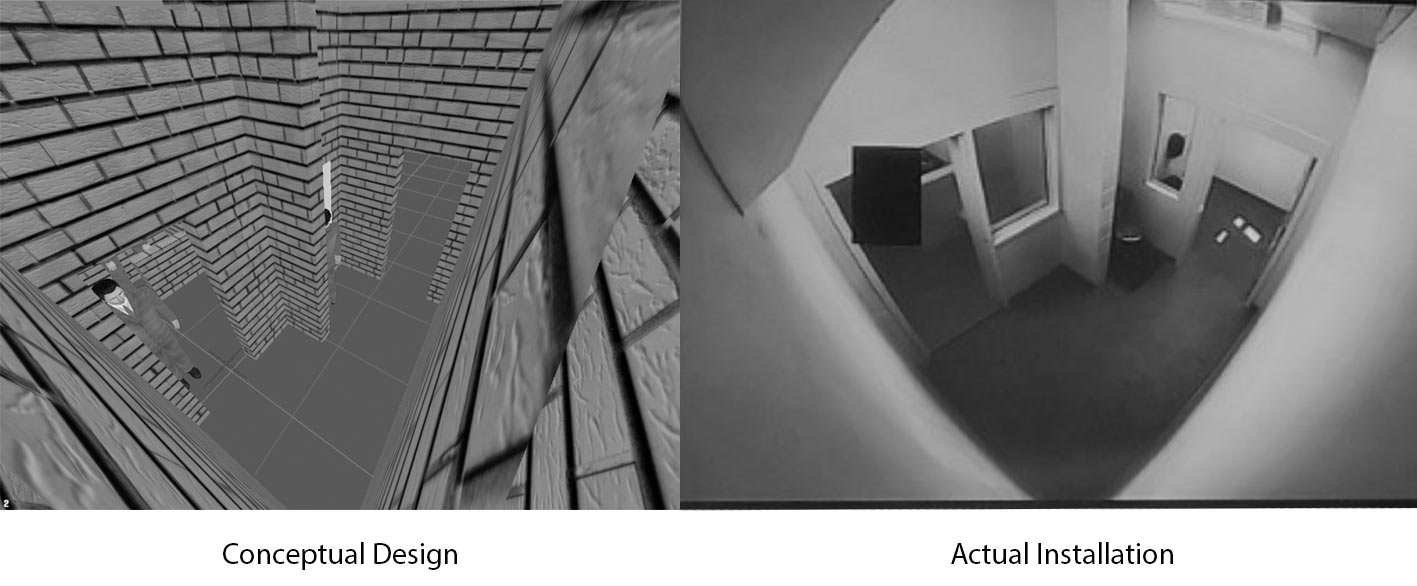
Avoid the many pitfalls and risks of improperly implemented solutions and equipment by leveraging our subject-matter expertise and support for all aspects of your construction and post-construction project phases. We help ensure your security solution is implemented in compliance with design and contract documents, and all submittals, inspections, and reviews are compliant with your related internal standards, industry standards, and best practices.
Define Requirements
Whether you have a new, existing, or a retrofit security project, we work with you to capture, review, analyze, evaluate and define the security requirements, business processes and overall needs. From baseline to advanced security requirements, we help you capture the many related elements and essential dependencies to define the scope, optimize your investment, and align your project with your overall business goals.
Design Development (SD, DD)
Maximize your investment and security resources with value-added design services from conception, development, to completion. Benefit from a comprehensive design and due diligence approach that brings together your technology, processes, and management across your physical, IT, Cyber and security management operations. A unified approach tailored to your business strategies, and to closing security gaps between programs, technologies, and processes.
Bid Documentation & Support
Leverage our expertise, and connections with manufacturers, system integrators and industry specialists for all stages of you project contractual and acquisition phases. Whether you are looking for the best procurement approach or looking for professionally-written RFP documentation, we can help you. Get the expert guidance, and robust industry-compliant contractual documentation that protects your investment and helps you compare, negotiate and select contracts fairly and transparently.
Project Management & Support
Avoid the many pitfalls and risks of improperly implemented solutions and equipment by leveraging our subject-matter expertise and support for all aspects of your construction and post-construction project phases. We help ensure your security solution is implemented in compliance with design and contract documents, and all submittals, inspections, and reviews are compliant with your related internal standards, industry standards, and best practices.
Comprehensive Design Expertise
It is imperative to consider the many related aspects, disciplines, and constraints for an effective and efficient security design in today's vast and converged world of security technologies, advanced threats, and the increasing legislative and compliance requirements.
Our planning and design services incorporate one or more of the following services:
Planning & Requirements Identification
Security Systems Design (Physical, Electronic, Information, IT/Cyber)
Procurement Support & Guidance Services
Subject Matter Expertise Support Services
Project Management Services
Advanced Video Surveillance Consultancy
Integration & Convergence Consultancy
Design Standards Development
Systems Assessment, Audit & Validation
Best Practices Gap Analysis
We offer both in-person or secure virtual consulting services where applicable.
If you did not find the specific service you are looking for please contact us to discuss your needs.
All it takes are few cheap parts that can be bought online to bypass some of the most common electronic access control systems in use by organizations today! Is your organization vulnerable?
Design & Planning Related Services
Click-on our additional services to learn more
 Electronic security systems play a significant role in modern security programs and their overall effectiveness in protecting assets and mitigating risks. However if improperly planned, selected, designed and implemented such systems can not only prove to be costly but can provide you and your organizations a false sense of security; hence increasing your overall risks and liabilities.
Electronic security systems play a significant role in modern security programs and their overall effectiveness in protecting assets and mitigating risks. However if improperly planned, selected, designed and implemented such systems can not only prove to be costly but can provide you and your organizations a false sense of security; hence increasing your overall risks and liabilities.
The rapid development of security technologies, the emerging trends of new disruptive service models, the growing convergence with building and connected systems, and most importantly their direct or indirect interconnection to corporate and external networks are increasing the risk surface to organizations and their security teams.
Our team of ASIS Board Certified Physical Security Professionals (PSP) and BICSI Certified Electronic Safety, and Security Designers (ESS) are highly qualified to help you plan, select, design, build and integrate the right systems and solutions that best fit your current and future security needs and protect your investment.
Experienced in hundreds of small to mega-scale projects across multiple markets, and certified to "expert-level" from various leading manufacturers, they have helped clients in achieving their objectives, delivering on their needs and exceeding their expectations. Our expertise and background go beyond just understanding the bits and bytes of technology and their business inter-dependencies to mine your actual needs, understand your overall requirements and provide you with valuable advice that spans the whole gamut of the physical, logical and security management domains. Ultimately, helping you protect your most valuable assets in the best way possible.
We work with you to design systems with the multi-discipline versatility to help maximize your benefits and minimize your long-term risks and costs. Our electronic security planning and design expertise span a variety of systems, their related IT infrastructures, and Cyber architectures; they include but are not limited to:
- Electronic access control systems
- Biometric devices
- Video surveillance systems (CCTV)
- Intrusion detection systems/Panic Alarms
- Electronic locking devices
- Emergency duress systems
- Electronic controlled physical barriers (Gates, Road Blockers, raised bollards)
- Visitor and incident management systems
- Converged logical and physical access
- Wired & Wireless Network Design
- Network Segmentation & Secure Architectures
- IP Intercom and integrated VOIP systems
- Special Security Screening Equipment
Other related design services are also available, please contact us to inquire about additional services, if we cannot provide it we can help guide you to trusted specialized consultants who can help.
 Design out the fear of crime through proper environmental planning and urban designs that make practical use of space and natural elements to improve access control, natural surveillance, and meet your security objectives from the get-go.
Design out the fear of crime through proper environmental planning and urban designs that make practical use of space and natural elements to improve access control, natural surveillance, and meet your security objectives from the get-go.
Whether you have an existing environment or conceptual built, we work closely with your architectural, design-built, and security teams to assist in outlining safe and secure environments that influence desired behaviors and the sense of safety and belonging.
Improve social interaction, territorial identity and your properties image with our CPTED services. Contact us today to learn more how we can help you utilize your environment to create defined and delineated public and private spaces and optimize your overall security program through manipulating the surrounding physical environment.
 We provide a variety of security consulting services for your Information Technology (IT) and Information Security (IS) to help you enhance your existing security program or develop a new one that meets your desired enterprise security goals and objectives.
We provide a variety of security consulting services for your Information Technology (IT) and Information Security (IS) to help you enhance your existing security program or develop a new one that meets your desired enterprise security goals and objectives.
Our certified information systems security professionals (CISSP's) cover a broad gamut of information technology and security domains. We provide current knowledge and advisory services that include but are not limited to the following:
- Network Security Architecture Review and Design (Wired & Wireless)
- Database (Provisioning, integration, migration, and hardening)
- Logical Access Control (Identity & Access Management)
- Data Storage Security (On-Premise, Cloud, Hybrid)
- Logical Security Operations
- Cyber-Physical Systems Security
- Virtualization security advisory
- Converged Physical & Logical Access Control
We bring you in-depth technical know-how, product knowledge, and business expertise to help you with your information security and information technology needs. Get in touch today and learn how our experts can help you!
 Very often we come across organizations having problems with inconsistent installation standards, incompatible products, contradicting zoning levels, and multiple systems running ineffectively side-by-side. Not only such scenarios cost time and money, but may also introduce risks, cause conflicts, and diminish the overall effectiveness of your security program.
Very often we come across organizations having problems with inconsistent installation standards, incompatible products, contradicting zoning levels, and multiple systems running ineffectively side-by-side. Not only such scenarios cost time and money, but may also introduce risks, cause conflicts, and diminish the overall effectiveness of your security program.
At Goldmark Security Consulting Inc., we help organizations, small or large, develop their security systems standards for existing, new or any on-going construction to ensure consistency of excellence, and desired security outcomes across all your offices, buildings, and facilities.
Whether you have enough resources to develop your own or looking for subject matter expertise we help you either in developing, reviewing or just updating your security systems standards which typically include but is not limited to:
- Physical Security Barriers
- Security Lighting
- Security Signage
- Security Layering and Zoning
- Security Systems installation details
- Security Systems product selection and diligence
- Information Security Controls
- Systems Configurations & Documentation Standards
- Cyber Security Controls
- Security Control Console/Center
- Secure Rooms, Guest Reception Areas, Equipment Rooms, and others...
Our multi-disciplinary approach helps in dismantling any siloed approach to creating a security systems standard that seals the gaps between interdependent disciplines, meets your business requirements and ensures consistency throughout your organization no matter how distributed or diverse. Contact us to learn more about our service and how we can help you and your internal team develop or update your security standards today.
 Understanding the industry cost models, keeping up-to-date with the emerging security technology trends, vulnerabilities, systems incompatibilities, licensing and legislative requirements, and vendor qualifications are just a few of the many and sometimes overwhelming factors that organizations and security managers go through during a security project procurement process.
Understanding the industry cost models, keeping up-to-date with the emerging security technology trends, vulnerabilities, systems incompatibilities, licensing and legislative requirements, and vendor qualifications are just a few of the many and sometimes overwhelming factors that organizations and security managers go through during a security project procurement process.
At Goldmark Security Consulting Inc., our board certified independent security consultants take on the heavy lifting for you by providing current security industry and expert products insights, the right skills, in-depth and up-to-date technical knowledge and professional advisory services to meet your security procurement and implementation needs.
We provide you with the professional expertise and assistance for qualifying vendors and bidders, issuing requests for information (RFI's), preparing a competitive bid package, attending and leading pre-bid meetings and site walk-throughs, reviewing submissions and providing objective recommendations on shortlisted bidders, negotiating proposals and making defensible recommendations for final vendor selection.
Our implementation advisory and project support services, offered at the construction phase of your project, ensure that the security systems installed and submitted project documentation are in accordance with specifications and highest industry standards. The implementation support typically includes but is not limited to the following services:
- Leading project stages including project kick-off, construction, and close-out meetings
- Attending construction and coordination meetings
- Reviewing shop drawings
- Responding to RFI's
- Issuing RFC's
- Inspection and witness testing
- Issuing punch list
- Reviewing invoices and issuing change orders
- Reviewing O&M and project close-out documentation
Contact us today to ensure your security systems are selected to match your requirements and are implemented professionally on time and within budget with the assistance of our certified independent consultants.
Avoid costly mistakes, recurring services, and unnecessary equipment! Get practical, effective, and justifiable solutions tailored to your organization's risks and needs.
Our Latest Articles
How to marry physical and logical security into a cohesive plan
Over the past five years, Canadian businesses have seen the threat of hacktivism, cyber extortion and the incidences of data breaches grow exponentially. No industry is immune to these threats, not...
Threat, Risk, & Vulnerability Assessment
Security Master Planning
Program Evaluation & Gap Analysis
Policies, Procedures & Standards
Cyber Threat Mitigation Controls
Cloud Security Consulting
Systems Design & Project Management
Security Social Engineering Awareness Training
Security Audits & Technical Systems Evaluation
Procurement Support & Systems Inspection
Integrated & Converged Security Systems
External Audits (Physical & Logical)
Effective Security Solutions!
Effective Security
Through Breaking The "Silo" Approach!Learn More
Pentesting and network vulnerability assessments on your enterprise network & systems can help you meet compliance requirements.
However, without the basic controls to validate against, your investment may leave you with a document sitting around and even worse that can be discovered in a breach lawsuit.
Need to upgrade or install new security systems?
Need insights for your product or vendor choices?
Need baseline security measures for your business?
Frequently Asked Questions
An independent security consultant is a dedicated security professional who makes his/her living providing fee-based security advise and professional services to the client's best interests.
Unlike many professionals who are employed, sell, install products and collect directly or indirectly sales commissions from manufacturers and designate themselves the title; independent security consultants are not affiliated with any product, manufacturer or organization that sell or install security products and sell or provide guard services.
While there are no official set of requirements for someone to claim the title, independent security consultants who are members of the International Association of Professional Security Consultants (IAPSC) pass rigid membership requirements, including background checks, verification of industry certifications and credentials, related employment experience, educational history and competence.
IAPSC members are not affiliated with any product or service they may recommend, they are bound to adhere to the highest industry standards for professionalism and ethical conduct. As the most widely respected and recognized security consultant association in the industry, clients selecting IAPSC members are selecting from a unique group of professional, ethical and competent security consultants.
Security is a very complex and broad field, while we cover multiple security domains our services are strictly limited to consulting services only and does not include the following:
- Electrical engineering and code compliance services
- Blast modeling, planning and design
- Selling, installing, or servicing security equipment or products
- Selling or providing security guard, patrol or bodyguard services
- Conduct private investigations or performing background checks
- Selling, installing, or servicing computer, network, or cyber security products
- Providing fire engineering or health & safety consulting services
- Providing forensic consulting services
- Crowded space protection
- Hacking or illegal pen-testing services
- Executive protection services and technical bug sweeps
In the case where Goldmark Security Consulting is sub-contracted into a project by a service provider such as a systems integrator, guard company, architectural or engineering firm, product manufacturer or another security consulting firm, we may accept such projects only with the contractual terms and understanding by all parties that Goldmark Security Consulting professional advise will be independent and to the best interest of the end-user client. In no case will we alter our advice or provide recommendations that favor the vendor who recommended us if it is not in the client’s best interests.
We greatly value our independence and transparent commitment to our clients hence we explicitly reject any business arrangements that pose any potential for a conflict of interest.
Uncommon Resources Delivering Exceptional Value
Translate the many risk languages of cyber security, information security, physical security, and security management to one unified language, your bottom line business risk.
Not only we provide you with a holistic approach to your security needs, but our team of experts also bring in their years of diverse hands-on experience in the security and IT industry to provide effective solutions and maximize your return on investment.
Leverage our broader expertise and perspective for addressing your various security needs and enabling your intelligent business decisions.
Our Latest Articles
Our Latest Articles
Our Mission
Our mission is to help your business thrive by bringing to light your organizations security risks and helping you tackle them before they turn into a crisis.
Get the Best Solution To Your
Technical, Management, Information and Cyber Security Concerns!
Through a holistic security risk advisory approach, we help organizations like yours protect what matters the most.|

