Converged Security Controls
Physical | Cyber | Information
Mitigates Most Pervasive Attacks
Mapped To Many Cyber Security Frameworks
Prioritized With High-Payoff
Regularly Updated By Cyber Experts
Supported & Recommended
Convoluted threats in the cyber and physical worlds are a reality, capturing daily headlines and making the list of top risks for organizations.
At Goldmark Security Consulting Inc., we help organizations small or large with a prioritized, proven and recommended risk-based security controls that are practical, validated, and measurable.
Our GIAC certified auditors, and (ISC)² certified information security experts, will work closely with your organization to assess and develop tactical and strategic cyber and cyber-physical programs based on your security posture, cyber maturity level, resources, and budget.
Get your cyber security scorecard today, and protect your investment with leading security controls that are developed by cyber experts and endorsed by many regulatory bodies, businesses, and governments.
Cyber Security Maturity Program
Converged Security Services
No ultimate solution can be implemented to eliminate your information security risks. However, with the right approach and measures, we help empower you to proactively protect your critical data and information assets, mitigate your business risks, and prepare to embrace, respond and recover gracefully in the event of undesired cyber or information security breach.
Through your trusted partnership and our various services, we help you develop the right security programs and measures to secure the valuable information assets entrusted to you.
Our information security services incorporate one or more of the following:
Executive Security Briefings
Data Classification Advisory
Critical Controls Briefings
Cloud Security Advisory
Incident Response Assessment
Security Awareness Assessment
We offer both in-person or secure virtual consulting services where applicable.
If you did not find the specific service you are looking for please contact us to discuss your needs.
Related Services
Click-on our additional services to learn more
Companies spend millions of dollars on firewalls, encryption and secure access devices, and it’s money wasted, because none of these measures address the weakest link in the security chain Kevin Mitnick
CIS Critical Security Controls
Get The Right Support!
Don't waste your time and money, our certified critical controls experts will provide you with the right support and guidance.
Stay Ahead Of Cyber Threats!
Our cyber security advisory services are based on actual attack data and threats from a variety of public and private threat sources!
CIS Controls
As proud CIS Controls adopters, our certified experts are currently consulting commercially on the latest up-to-date release.
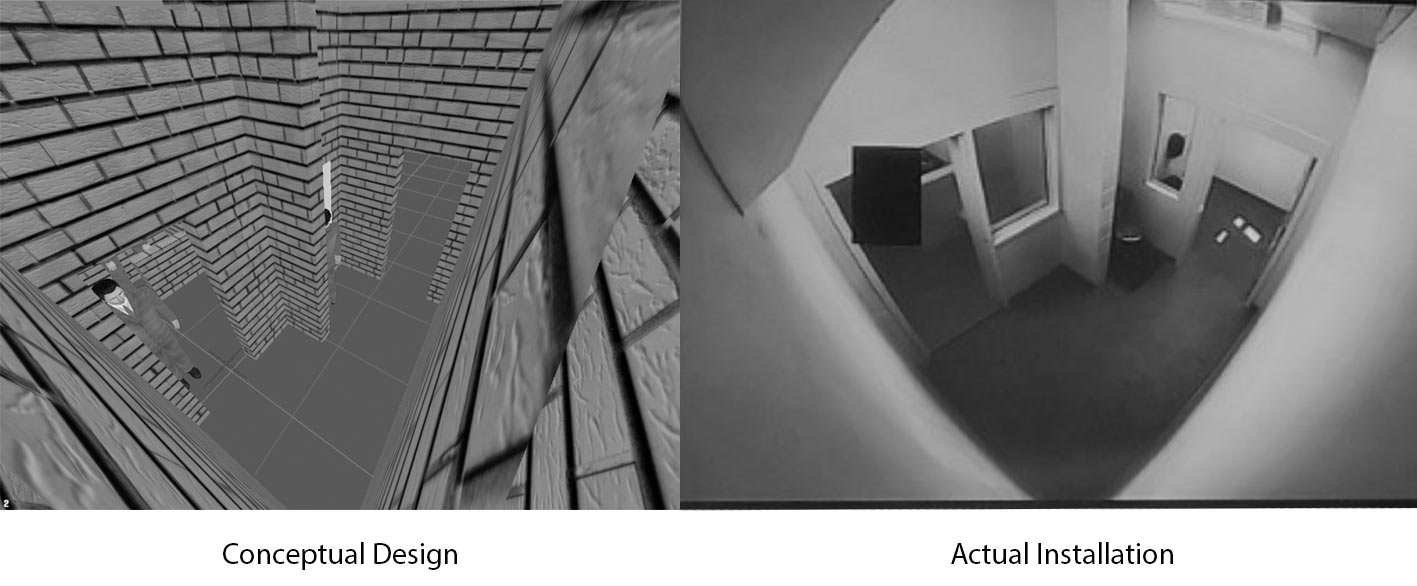
IoT Botnet- 25,000 CCTV Cameras Hacked to launch DDOS Attack The Hacker News, June 2016
Need to validate your cyber controls?
Need to evaluate your cyber-physical risks?
Need to prioritize your security choices?



 Cyber security is not limited to technical controls and measures. The weakest security link remains the human with all his or her emotional senses. With the increasing rates of "Phishing", "Vishing", and the many creative social engineering attacks and methods used today, your organization, employees and valuable assets remain vulnerable.
Cyber security is not limited to technical controls and measures. The weakest security link remains the human with all his or her emotional senses. With the increasing rates of "Phishing", "Vishing", and the many creative social engineering attacks and methods used today, your organization, employees and valuable assets remain vulnerable.
 Adopting cloud services is not a matter of if, it is only a matter of when. Sure this shift in technology has its positive and negative impacts on securing your information assets and providing the many benefits of cloud services. It not only stretches your boundary of defenses beyond the physical perimeters of your facilities it also brings with it many operating and governing challenges.
Adopting cloud services is not a matter of if, it is only a matter of when. Sure this shift in technology has its positive and negative impacts on securing your information assets and providing the many benefits of cloud services. It not only stretches your boundary of defenses beyond the physical perimeters of your facilities it also brings with it many operating and governing challenges. We provide a variety of security consulting services for your Information Technology (IT) and Information Security (IS) to help you enhance your existing security program or develop a new one that meets your desired enterprise security goals and objectives.
Our certified information systems security professionals (CISSP's) cover a broad gamut of information technology and security domains. We provide current knowledge and advisory services that include but are not limited to the following:
We provide a variety of security consulting services for your Information Technology (IT) and Information Security (IS) to help you enhance your existing security program or develop a new one that meets your desired enterprise security goals and objectives.
Our certified information systems security professionals (CISSP's) cover a broad gamut of information technology and security domains. We provide current knowledge and advisory services that include but are not limited to the following:
